What Is 2FA (Two-Factor Authentication)? How to Enable 2FA
In today’s world, security for your online accounts is a challenge. Even creating strong usernames and passwords can only protect your accounts so much. New computer technology is even more successful in hacking attempts, which exposes your information and puts you at risk. Because of this, many users choose to add an extra layer of security to their accounts with two-factor authentication, or 2FA.
What is 2FA?
2FA is a term you've likely seen in conversations about passwords and online security. But what is 2FA? 2FA, which is short for two-factor authentication, is a security method requiring users to submit two forms of identification or confirmation in order to log in to an account.
In some cases, it's also called multi-factor authentication (MFA). However, MFA requires at least two types of authentication whereas 2FA only requires two types of authentication. 2FA adds a second step to the login process; instead of just entering your password, you also must verify yourself with a code or key.
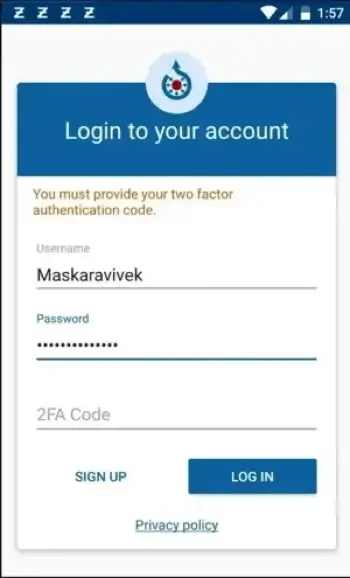
The two-step verification system doesn’t replace your username or password. You’ll still enter that information to log in to your account. 2FA simply provides an additional layer of security for online accounts, lessening the chances of hacking attacks or data loss incidents.
How does 2FA work?
With two-factor authentication, you use two different authentication methods to get into an online account. When you go to log in, you'll enter your password. However, you'll also be prompted to enter a code send to a secondary device or system, like your phone or email account.
When you set up your account or turned on two-factor authentication, you likely had to choose a communication method. These settings are saved and used to deliver your code each time you log in to your account.
This code is a one-time-use code that times out after a certain period has passed. This makes your account significantly more secure; you can't log in with just your username and password. You need the time-sensitive code too.
Types of 2FA
There are several different types of two-factor verification available on various platforms and apps. Some, like SMS- and email-based 2FA, are more commonly seen, but all forms serve the same purpose. These two-factor authentication methods improve your account security and keep your data safe.
SMS-based 2FA
SMS two-factor authentication is the most common method of 2FA. Once the user has entered their username and password, the website or app sends a text message to the user that includes a unique one-time passcode (OTP). The user receives the message, enters the OTP into the program, and has access to their account.
This type of 2FA is widespread and convenient; in recent years, Apple has even added a feature that allows users to automatically fill in verification codes sent via iMessage. However, because of the vulnerability of SMS and phone calls as a medium, SMS-based 2FA is also considered to be the most vulnerable type. It works well for lesser accounts, but for important accounts like banking or email, consider using a different method of 2FA.
Email-based 2FA
Email two-factor authentication follows the same procedure as SMS-based 2FA; however, instead of the code arriving in your messages, it arrives in your email inbox. This is a more secure method, as you need to log in to your email with your email password in order to be able to access the code. It’s also convenient, as many people have their email on their phone or laptop when trying to log in to their other accounts with 2FA.
Push notifications for 2FA
Instead of using an external communication method, like email or text, many websites opt to send users a push notification on their devices when they attempt to log in. The user can get the notification, view the details, and choose whether to approve or deny access to the account for which the login attempt is taking place.
This type of 2FA is arguably simpler than SMS- or email-based, as users don’t need to wait for codes or open their email to enter them. It also eliminates the potential for phishing attacks to occur in the middle of the login attempt because this method establishes a direct, secure connection between the account and the device. Push notifications are secure and more user-friendly for those who opt into 2FA.
Software tokens for 2FA
Software tokens or keys are another option for users opting in to 2FA. These often come in the form of authenticator apps. Authenticator apps work by generating single-use codes, used to confirm your identity at login.
You must link the websites to the app on your mobile device, but then the sites generate keys, which get saved to the authenticator app. The keys, typically displayed as QR codes, are time-based and are scannable to your phone within a few seconds.
When you log in again to a website, check the app for the code. If the access key code matches the website’s, you will successfully be logged in, just like with a text message. Google Authenticator is a good choice for an authenticator app; for Android or Google account users, it can even be used directly through a Google account in place of calls or texts. Software tokens are accessible and easy to use for all users.
Hardware keys for 2FA
Hardware keys are the oldest form of two-factor authentication and the only kind that requires an additional physical device. They’re small, like a dongle or key fob, and generate new codes every few seconds for users trying to log into their accounts. Some plug into a user’s computer, while others just generate codes for the user to read.
While they work like other 2FA methods, they’re arguably not the safest, as they’re easy to lose and not hack-proof. However, hardware tokens don’t rely on wireless access, which is helpful for those who have unstable wireless connections.
Advantages of two-factor authentication
Two-factor authentication is an excellent security measure for all users, no matter how often you go online. Consider the following benefits of using 2FA:
- It improves account security. Using 2FA, you have a significantly lower chance of becoming a hacker victim. 2019 reports from Microsoft and Google reported that 2FA blocked roughly 99% of all automated attacks, which is a remarkable statistic. For accounts that contain a lot of personal information or sensitive data, you want that level of security.
- 2FA alerts can serve as security alerts. Two-step verification texts and phone codes also serve as a sort of security alert on their own. If you get a text containing a code for an Amazon login out of the blue, it’s possible that someone else is attempting to access your account. You can go in and change your password. Had you left 2FA disabled, your account may have been successfully hacked.
- It fights against identity theft and fraud. When someone hacks your account, they can access all the personal information you have on file. This increases your risk for fraud, identity theft, and other information-based crimes.
- Businesses save money on technical support and services. Blocking some potential attacks means fewer resources spent deflecting or cleaning up security incidents. From a business standpoint, this saves valuable money, time, and resources.
Whether you’re an individual or in charge of a large corporation, enacting two-step verification on your accounts and network provides major security benefits.
Disadvantages of two-factor authentication
There are no drawbacks to using two-factor authentication from a security standpoint. It keeps your accounts secure, helps protect against identity theft and fraud, and is easy to enable.
However, it does make logging into your accounts a slightly longer process. The added security step means 2FA is not the most convenient login method, even though it may be the most secure.
If convenience is your number-one priority, then consider using a password manager instead; it offers secure password storage for easy logins. But even a password manager can’t provide the same level of security that two-factor authentication can.
Remember that security isn’t always the most convenient option. Hackers rely on the fact that online users don’t keep their accounts secure. Taking a few extra seconds to use a 2FA key or code is worth it in the end.
How to get 2FA
Knowing how to enable 2FA isn't as difficult as it may seem. Many accounts with sensitive information automatically use two-factor authentication methods. Banking websites and apps, for example, often send a code to the user when they log on to their account as an added security measure. However, other accounts – like Apple’s Apple ID – only require a verification code when signing in with a new device.
Each app that offers two-step verification will enable the verification process differently. Check your account settings or security settings to find out how to enable 2FA on various apps or websites. However, we’ve detailed the steps below for how to enable 2FA on your Google account, Apple ID, or Android phone. If you want to know how to disable two-factor authentication, simply follow the steps below for your device and turn 2FA off instead of on.

Enable 2FA on Google account
To turn on two-factor authentication on your Google account, follow these steps:
- Open your Google account. If you’re in Chrome, do this by clicking on your account icon in the top-right corner and selecting Manage your Google account.
- In the navigation panel, select Security.
- Under Signing in to Google, select 2-Step Verification and then Get Started.
- Follow the on-screen prompts. You will be asked to enter your password and choose a verification method. After setting up the verification method, you can click the Turn On button to enable 2FA.
Enable 2FA for Apple devices
To turn on two-factor authentication on your Apple devices, follow these steps:
For iPhone, iPad, or iPod Touch:
- Go to Settings.
- Select your Apple ID account and choose Password & Security. Enter your Apple ID password if prompted.
- Tap Turn On Two-Factor Authentication.
- Tap Continue.
- Enter the phone number that you want to use as your secure phone number for verification codes and select Next.
- Enter the verification code to verify the phone number and turn on two-factor authentication.
For Mac:
- Choose the Apple menu and find System Settings.
- Click your Apple ID and choose Password & Security.
- Next to Two-Factor Authentication, click Turn On.
- Follow the prompts to enter your phone number and verify your number.
Enable 2FA for Android phones
To enable two-factor authentication on Android mobile phones, follow these steps:
- Open your Google account.
- In the navigation panel, select Security.
- Under “Signing in to Google,” select 2-Step Verification and tap Get Started.
- Follow the on-screen steps.
Is 2FA secure?
Yes, 2FA is secure. It provides an extra level of security to your accounts. However, keep in mind that no security method is perfect; enabling a two-step verification process does not mean users can forgo other methods of security or pay less attention to the security of their accounts.
Furthermore, some methods of 2FA are more secure than others. A software key, for example, is more secure than SMS-based two-factor verification.
Even if you enable 2FA, make sure that you avoid visiting suspicious websites or clicking email links that could potentially hack your email or get access to your phone number. If a hacker has access to your phone or email, along with stolen passwords, they can gain access to your accounts regardless.
Should I use 2FA?
We recommend that you use 2FA whenever possible. Though it’s not a perfect system, it provides better security than usernames and passwords alone. Your accounts will be less vulnerable to hackers and other cybercriminals. Many security architectures, such as Zero Trust Network Access, use 2FA in their structure for additional protection.
For minor accounts that you're not worried about, you can probably take the risk and turn off two-factor authentication. But like we said above, it's an excellent layer of security to add onto any account that has sensitive information. Consider what information the account holds before switching off 2FA.
Whether you choose email authentication, text message or call authentication, or an authenticator app, 2FA is a great security measure to enable on your accounts. It reduces your risk of data breaches and increases your safety online.