What Is TCP/IP? A Guide to Protocols and Layers
The TCP/IP protocol plays a pivotal role in digital communications. Everything from sending emails to uploading content is governed by TCP/IP; it serves as the standard for the Internet. In this article, explore the five-layer TCP/IP model to learn what it is and how each of the TCP/IP layers contributes to the model as a whole.
What is TCP/IP?
TCP/IP stands for Transmission Control Protocol (TCP) and Internet Protocol (IP). It is a set of rules that allow computers to communicate across a network. Countless online activities involve computers communicating with each other. Sending emails, video streaming, Zoom calls, and uploading content to the Internet are just a few examples of processes that require communication between devices over some kind of network.
When two computers communicate, they must know several things before transmission commences.
How does communication start? Whose turn is it to send data? How do devices know their message is sent properly? How does the conversation end?
Computers decide these things through protocols, essentially agreements between devices regarding how transmission will happen. A universal standard was necessary to ensure that each computer used the protocols. TCP/IP is that standard set of protocols that allows for device communication over a computer network.
What are the layers of TCP/IP?
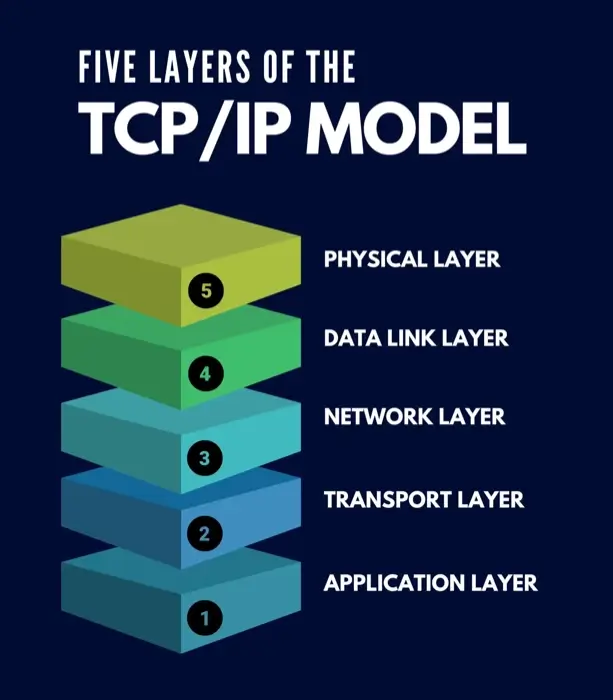
The TCP/IP reference model is divided into five layers, but some consider it to have four layers by combining two of the layers in the five-layer model. The five layers are:
- Application layer
- Transport layer
- Network layer
- Data link layer
- Physical layer
Each layer has different responsibilities, and all work together for successful communication across networks.
Layer 1: Application layer
The application layer deals with communication between the sender and the receiver. It ensures that the data reaches the receiver error-free and protects the upper-layer applications from data complexity. Several protocols exist in this layer.
The first of these protocols are HTTP and HTTPS. These protocols may look recognizable, as they are at the start of many URLs that access websites. HTTP stands for Hypertext Transfer Protocol, while HTTPS stands for Hypertext Transfer Protocol-Secure. They are used to manage communication between web browsers and servers.
The next protocol is SSH, which stands for Secure Shell. It is a terminal emulation software that emulates or displays videos within a certain area on the computer. It can maintain an encrypted connection over a TCP/IP session, which better guarantees the security and privacy of your data and information.
The final application layer protocol is NTP, or the Network Time Protocol. It synchronizes the clocks on every device with one standard time source. It is useful and preferred in situations like banking transactions.
Layer 2: Transport layer
When data travels from one device to another, it splits into groups called packets. Each data packet is a specific size. They must all arrive at their destination and reassemble to form the full message sent. The transport layer exchanges data receipt acknowledgments and retransmits missing data packets to ensure that packets arrive in order and without being corrupted.
The model uses two protocols at the transport layer: TCP and UDP. TCP stands for Transmission Control Protocol, and it transmits data in a way that appears more like character-by-character transmission than division into packets. Using TCP, devices can communicate with each other as though they were physically connected in a circuit.
UDP stands for User Datagram Protocol, and it provides a delivery service for datagrams - a specific type of packet used by some devices. Devices use UDP when they need to send a smaller amount of data because it eliminates the process of validating a connection between the devices.
Layer 3: Network layer
The network layer defines protocols that head the logical data transmission over a network. The first is IP, or Internet Protocol, which looks at the headers of each data packet and reads the IP address listed on it. That is the packet’s destination, and the IP protocol then delivers the packet to the device with that address.
The second protocol is ICMP, Internet Control Message Protocol, which provides people with information about network problems they are experiencing. The final protocol is ARP, Address Resolution Protocol, which finds the device's hardware address using its known IP address.
Layer 4: Data link layer
The data link layer defines a packet’s network protocol type. Examples include Point-to-Point Protocol (PPP) and Ethernet protocols. PPP is a communication protocol that provides loop connection authentication, transmission encryption, and data protection. Ethernet protocols encapsulate and decapsulate all data sent to the fourth layer from other layers.
The data link layer also resolves transmission errors and a service called framing. Frames are the units of digital transmission. Framing enables a data type to the sender for transmission to a receiver.
Layer 5: Physical layer
Finally, the physical layer is a group of applications that need network communications. This layer generates data that is transmitted and requests connections for those transmissions. It also defines the transmission medium and method of communication between two devices.
How does TCP/IP work?
TCP/IP uses a client-server communication model, meaning that one device – typically the user – requests information or sends updates to another computer, the server. The server then responds to the request, offering services like sending a webpage or updating a database.
In TCP/IP, client requests are always considered new or stateless, meaning that they aren’t related to any other requests. This opens up network pathways for the constant delivery of information.
The transport layer, however, is what is called stateful, meaning that some requests are related to one another. This layer sends out a message, and the connection remains constant until it receives and reassembles every packet of information into the original message.
What is TCP/IP used for?
TCP/IP has many useful applications. Most generally, it enables communication between multiple devices connected on a network. It also provides connections and routing protocols between networks to connect devices separated by great distances or simply connected to different networks.
Due to the power of TCP/IP protocols, devices hundreds of miles apart can seamlessly communicate. It can also provide remote logins for file transfers; in simpler terms, it can deliver emails, deliver and provide access to websites, and remotely access a server’s file system.
However, the TCP/IP system's true novelty is that it describes how data flows from one state to another. The physical layer is real and tangible, while the application level is abstract and difficult to understand. TCP/IP provides an easy-to-understand model of how information travels and changes form from one of these layers to another.
Why should I use TCP/IP?
There are many advantages to using the TCP/IP system. It helps create strong connections not just between different devices, but between different types of devices, and it supports many routing protocols for traversing between networks.
TCP/IP also functions independently of a device’s operating system, allowing it to be operated independently. Plus, the scalable client-server architecture means that it can serve many clients without having to worry about a lack of servers. Finally, it is lightweight and doesn’t overload or overwork your device during communications.
However, TCP/IP is not a perfect system. Without technical knowledge and experience, setting up and managing the system can seem complicated. The protocols it provides are not easy to remove once they have been installed, and it can be hard to clearly distinguish between its services, protocols, and interfaces. TCP/IP is also particularly vulnerable to specific computer security threats that can result in exploited data.
What other network models exist?
The Open Systems Interconnect model, or OSI model, was the first standard model of Internet protocols for communication over a network. OSI uses a seven-layer model to visualize communication between network devices, rather than TCP/IP’s simplified five-layer model. However, the TCP/IP and OSI model layers are similar. The OSI model layers are as follows:
- Application layer
- Presentation layer
- Session layer
- Transport layer
- Network layer
- Data link layer
- Physical layer
While the modern Internet is based on the TCP/IP model, the OSI model remains useful for visualizing and understanding network operations.
What is the difference between the TCP/IP model and the OSI model?
Each of the TCP/IP layers essentially matches to the function of layers in the OSI model. The application layer of TCP/IP performs functions of the application, presentation, and session layers of the OSI model. The rest match up based on their names: network layer to network layer, transport layer to transport layer, and so on.
However, while they may have many similarities, the two models have many differences as well. For example, the TCP/IP model is more reliable than the OSI model, and it doesn’t have very strict boundaries of communication. The OSI model, on the other hand, does.
TCP/IP emerged from first creating protocols themselves, and then creating a model to explain them. OSI developed in the reverse order – a model followed by protocols to fit the model. This makes it less versatile and more structurally rigid. For this reason, most users favor TCP/IP and consider it the basis of network communication for the modern Internet.
Frequently asked questions
What is the difference between TCP/IP and UDP?
The Transmission Control Protocol/Internet Protocol (TCP/IP) and the User Datagram Protocol (UDP) are both transport layer protocols, but the primary difference is that UDP is a connectionless protocol. With TCP/IP, both ends of the communication link must always be connected. With UDP, no connection is needed for sending and receiving data.
What is a TCP/IP port?
A TCP/IP port is a virtual endpoint that facilitates the communication between devices over a network through TCP/IP.