How to Avoid Phishing Attacks: Red Flags to Watch For
As you've probably heard, phishing is one of the most often-used techniques hackers use to break into devices or computer systems to steal sensitive data like credit card numbers, login credentials, or other valuable information. And as you've also probably heard, the best defense against phishing attacks is to use "common sense." But what does that actually look like? Phishing attacks present in a variety of ways. It can be hard to identify exactly what's a phishing scam and what's just a regular email or phone call. This article will show you some specific, tell-tale signs that the message you received might be a phishing scam.
What is phishing?
Phishing is a cybercrime that targets individuals via email, phone, text message, or social media direct message. It is a form of social engineering.
The goal is to lure victims into giving up their personal information or sensitive data like bank account logins, credit card details, passwords, or Social Security numbers. The messages are disguised in order to appear legitimate. Victims often don't realize that they are interacting with a hacker rather than a legitimate organization.
Once the cybercriminals have the information, they can use it to access victims' personal accounts, commit identity theft, or drain their bank accounts. These phishing campaigns are successful before the victim even realizes that they have been phished, which makes it harder to get back assets or keep information safe.
The 2022 Verizon security report found that 36% of all data breaches involve phishing attacks. Given how serious data breaches are – the same report found that the average business loses $30,000 when their email is compromised and financial information lost, and 64% of organizations have experienced a phishing attack in the past year – it’s critical to be on alert for phishing attacks.
Three steps to identify phishing emails
96% of all phishing attacks are via email. This means that though robocalls and fake websites do need to be on Internet users' radars, suspicious emails are the biggest threat and most common type of phishing. Though many email servers have services that block spam emails and email spoofing, according to a survey in 2020, 1 in every 4,200 emails is a phishing email, meaning that there are still messages that make it through to users' inboxes.
Though it sounds intimidating, recognizing phishing emails is simple if you know what to look for. The best way to check if an email is legitimate or not is by analyzing the sender address, links, and content.
Examine the sender’s email address
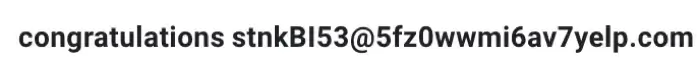
The sender's name may appear to be a legitimate company, but it's important to also look at the sender's email address. Take the example below; though the email is just entitled "Congratulations," clicking on the name reveals that the actual email address is suspicious. Even though ‘yelp.com’ is in the email address, the random string of letters and numbers preceding it indicates the email is not legitimate.
Even if the email address isn’t a random string of characters, make sure the email address is from the correct company and correct department. Keep in mind that most big companies have their own email domain. If you get an email that claims to be from your bank’s customer support and the address is ‘[email protected],’ it’s likely a scam.
If you receive an email with an unknown sender, don’t open it. These are very likely scam or spam messages.
Analyze the links and attachments within the email
Phishing emails, like spoofing emails, typically include links. Once the victim clicks on a link, it downloads malware onto their device or takes them to a fake website, which steals their personal information.
You never want to click on a link within an email without knowing where it will take you. In your desktop email program, you can hover over a link to see where it will go once clicked, like in the image below.
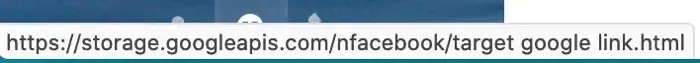
Paste the link into a note or document so you can view it without the risk of going to the actual site. In this case, the link doesn't indicate whether the email is a scam. If a link directs you to an obscure site, be wary.
If an email includes a lot of unnecessary attachments or links, this is also a sign that the email is a phishing attack. Never open an attachment you don't expect; these can also download malware to your device.![]()
Consider the content
Often, you can identify a phishing email by the above factors alone. However, if you’re still not sure, read through the content of the email. Look for language of urgency; is the sender creating a sense of urgency by claiming you need to click a link, reply, or download an attachment right now? Are they threatening jail time or monetary loss if you don’t act?
Rest assured that your bank will not hinge the security of your account over whether you download a file. Language like this indicates that the email is a phishing attempt, as the scammer hopes to push you to act.
Check the body of the email for other subtle red flags, like typos. Emails from legitimate companies are proofread before sending; if your email is riddled with spelling or grammatical mistakes, it’s likely a phishing email. Check that the organization or company name is spelled correctly and that the logo looks correct. Hackers often misspell big companies’ names in order to pose as them.
How to stop phishing emails
While your first thought may be to unsubscribe from phishing emails, that may not be the best course of action. Phishing emails are often sent out en masse; unsubscribing only shows that your email account is active, meaning the scammers are likely to send more messages to your address in the future. Instead, delete the messages without interacting or responding.
To prevent phishing scams in the future, your best bet is using a secure email gateway, which blocks malicious or phishing emails before they reach your inbox. Use a VPN or proxy server to mask your IP address, as bad actors can use your public IP address to deliver attacks. Install an antivirus software program as well; if you do fall victim to phishing attacks, this will limit the impact of the attack.
How to mark messages as spam in popular email servers
If you receive spam frequently and want to rid it from your inbox, there are ways to mark an email – or email sender – as “Spam.” This separates it from the rest of your inbox, allowing you to go through and delete it without having an inbox full of spam. Below are the steps for marking messages as spam in Gmail, Outlook, Yahoo, and iCloud.
Mark messages as spam in Gmail
To mark an email message as spam in Gmail, both in the desktop application and on Android phones, follow these steps:
- Open the Gmail application.
- Select one or more emails that you believe to be spam.
- Go to the navigation bar at the top of your email, just below the search bar.
- Click on the Report Spam symbol, which appears as an exclamation mark within an octagon.
Mark messages as spam in Outlook
To mark an email message as spam in Outlook, follow these steps:
- Open Outlook.
- Select the email or emails that you believe to be spam.
- Go to the Home tab and click on the Delete
- Select the Junk
- Choose Report as Junk.
Mark messages as spam in Yahoo
To mark an email message as spam in Yahoo, follow these steps:
- Open Yahoo.
- Select the email or emails that you believe to be spam.
- Select Spam in the toolbar above your inbox.
Mark messages as spam in iCloud mail
To mark an email message as spam in iCloud mail on a Mac, follow these steps:
- Open the Mail app.
- Select the email or emails you believe to be spam.
- Click the Junk button in the Mail toolbar.
To mark an email message as spam in iCloud mail on an iPhone, iPad, or iPod Touch, follow these steps:
- Open the Mail app.
- Swipe left on the message and tap More.
- Tap Move to Junk.
Report phishing emails
Reporting phishing scams is not necessary in every case, but it’s a good practice; reporting phishing attempts helps keep yourself and others safer. To report a phishing scam, you can first go to the official website of the company that the email claims to be from. Sometimes, these sites have a section dedicated to spam or phishing email reports. If you can’t find a way to report the email directly on the website in question, simply forward the email to abuse@(companyname).com. These email addresses are set to receive email phishing reports.
If you are a victim of identity theft after a phishing attack, contact your local law enforcement. You can also report phishing scams to the Internet Crime Complaint Center or the Federal Trade Commission. Forward phishing emails to [email protected], which is the Anti-Phishing Working Group, and report it to the FTC at FTC.gov/Complaint.
Frequently asked questions
What is vishing? How is it different from phishing?
Vishing is not entirely different from phishing; rather, it's a specific subcategory of phishing attack. It refers to voice phishing, or phishing via phone calls. Vishing attacks involve a caller claiming to be from some sort of authoritative agency, whether it be your bank, the government, or the IRS.
They insist that you give personal information over the phone in order to check on fraudulent activity, but these claims are entirely false. Just like with traditional email phishing, the cybercriminal wants to bait information from the victim in order to get access to their personal information and accounts.
What is smishing?
Smishing, which refers to text message or SMS phishing, works the same way as vishing or phishing. The victim gets a text message asking for sensitive information or with a link to click, which then leads to a malicious website or downloads a virus onto the device.
What is spear phishing?
Spear phishing is a specific, targeted phishing attack against one person or a few select people. Hackers send phishing messages out en masse to all groups of people. But they direct spear phishing attacks towards an individual. The attacks can be via text, telephone call, or email, but the intent is, as with general phishing, to get information, like account numbers or personal data, from a target.
These spear phishing attacks are typically more target-specific. They may appear as an email from an individual's CEO or boss. It could be a text from a sender who appears to be Amazon. With spear phishing, the fact that it's an attack may be less obvious, so users must practice extra vigilance.
Don't be afraid to confirm that the sender is who they say they are. Email your CEO (from a new email thread - don't just respond back) asking them to confirm the information in the suspicious email. Check your Amazon account to get the tracking link from there instead of the text.